FAQ's
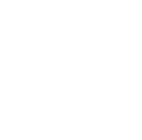
- Data privacy security ensures personal and business data is collected, processed, and stored safely. It helps organizations comply with regulations while building trust with customers by safeguarding sensitive information.
- Data loss prevention security prevents unauthorized sharing or leakage of sensitive information. It helps organizations monitor data flow, block suspicious activities, and ensure compliance with data protection policies.
- A next gen firewall provides advanced features like intrusion prevention, sandboxing, and application control, unlike a traditional firewall, which focuses mainly on traffic filtering and basic protection.
- Secure access service edge (SASE solutions) combine networking and security into one framework. They provide secure, fast, and scalable connectivity between users, branches, and data centers.
- Businesses need email security solutions because most cyberattacks begin with phishing, spam, or ransomware emails. With advanced email protection and spam protection, organizations secure users, systems, and sensitive data.